The offensive side of the fence.
Exploit Pack's new v18 is ready for download, try it now.

Our Pricing Options
Choose the tier option that is right for you:
Full license: The real deal. Exploit Pack contains all the exploits you could possibly find out there: A set of 39.500+ exploits + Zero Days, Implants and post-exploitation modules. You can be sure that your next pentest will become unstoppable with Exploit Pack in your arsenal of tools. All platforms are supported: Windows, Linux, Unix, Minix, SCO, Solaris, OSX and you can even target mobile and web.
What's also included: A full license of Exploit Pack Framework also includes access to monthly updates, live online training and technical support available throughout the entire duration of the license.
Delivery: Personal keys are delivered via email within 24 hours of purchase and linked to the email address used during the purchase.
Do you need a quotation? Email us
⦁ We do not issue refunds for our products once the order is confirmed and the product is digitally sent.
⦁ Please be aware that all issued licenses cannot be modified or sent to a different email address at any later stage.
⦁ We recommend contacting us for assistance if you experience any issues receiving or downloading our products.
Technical support for lifetime licenses is valid for a period of three years from the date of purchase. During this time frame, customers will receive assistance and guidance pertaining to the product's functionality, troubleshooting, and maintenance.
1-year Exploit Pack + 1-year Control Pack
€1800
1 year - (1 user license)
Discounted price
- ✔ Discounted price
- ✔ Exploit Pack + Control Pack full licenses + updates.
- ✔ Monthly updates
- ✔ Over 39.500 exploits
- ✔ Zero day exploits
- ✔ Monthly Zero day exploits from our lab along with video tutorials
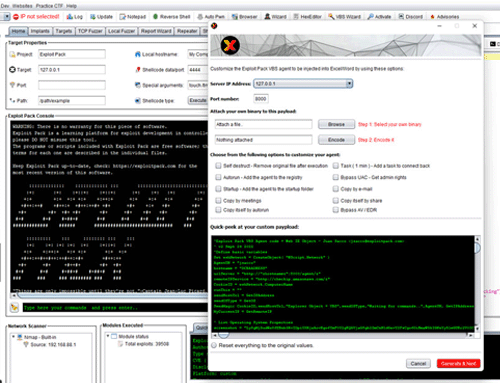
- ✔ Exploit editor ( reconfigure, modify and add new exploits )
- ✔ Exploit Finder (by OS, type, service, etc.)
- ✔ Local Fuzzer
- ✔ Remote Fuzzer
- ✔ Web attacks
- ✔ Post-Exploitation
- ✔ Remote control
- ✔ Automated attacks
- ✔ Network scanner
- ✔ Targets management
- ✔ Hexa editor
- ✔ Reverse shells ( include a custom shellcode or convert into an executable file )
- ✔ Live online training
- ✔ Technical support
One-year license - Exploit Pack
€950
1 year - (1 user license)
Regular full license
- ✖ Discounted price
- ✔ Exploit Pack full license + updates.
- ✔ Monthly updates
- ✔ Over 39.500 exploits
- ✔ Zero day exploits
- ✔ Monthly Zero day exploits from our lab along with video tutorials
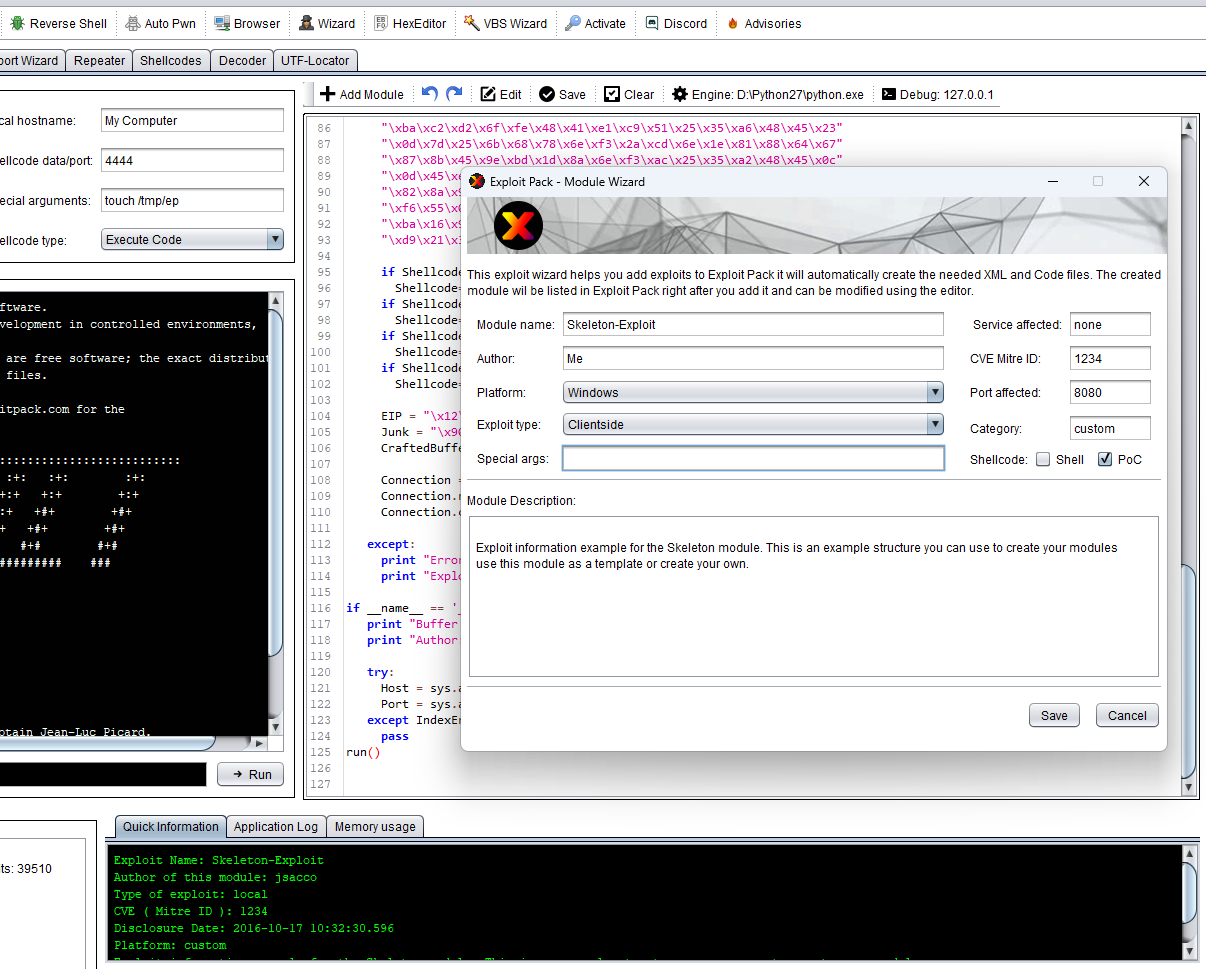
- ✔ Exploit editor ( reconfigure, modify and add new exploits )
- ✔ Exploit Finder (by OS, type, service, etc.)
- ✔ Local Fuzzer
- ✔ Remote Fuzzer
- ✔ Web attacks
- ✔ Post-Exploitation
- ✔ Remote control
- ✔ Automated attacks
- ✔ Network scanner
- ✔ Targets management
- ✔ Hexa editor
- ✔ Reverse shells ( include a custom shellcode or convert into an executable file )
- ✔ Live online training
- ✔ Technical support
Uncover and exploit security weaknesses.
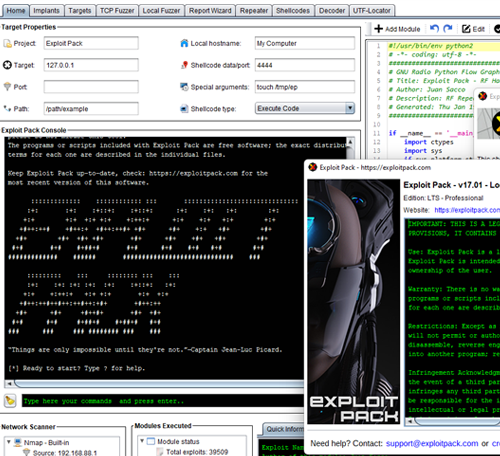
Exploit Pack is an advanced exploitation framework that will allow you to develop your own exploits or make use of the zero-days from our lab among the included 39.500+ public exploits.
Exploit Pack's features and customization options make it a must-have tool for any security professional seeking to test the defenses of an organization's digital infrastructure. Exploit Pack is weekly updated and backed by a team of experienced developers and penetration testers, that way, it remains always up-to-date with the latest threats.
Take full control of your target and remain under the radar, don't stop at simulation. We help penetration testers and cyber security professionals around the world achieve results no other tools can.
How can Exploit Pack help you
Exploit Pack has been designed by an experienced team of software developers and exploit writers to automate processes with the latest techniques so that security professionals can focus on what's really important:
The threat.
Adapt, disrupt and mitigate
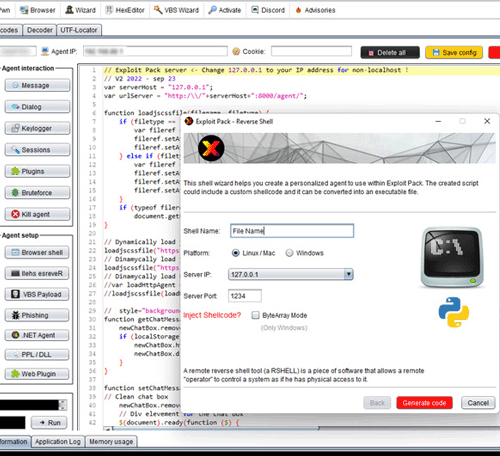
Adapt your exploit code on the fly, take full control of your target, remain under the radar of the most modern sensors and detection rules. Mitigate and report your attack, then evolve, fix and improve your target.
Don't simulate, attack and take control
 After a successful exploitation, make use of our agents, bypass all modern AVs and EDRs and then obtain persistence and exfiltrate data under the radar. Become silent with Exploit Pack.
After a successful exploitation, make use of our agents, bypass all modern AVs and EDRs and then obtain persistence and exfiltrate data under the radar. Become silent with Exploit Pack.
Technical support and Training
 Never get stuck, your license includes technical support and consultation during your next project. Also, join our online training ready for you and your team. We are here to help you achieve results and improve your pentesting capabilities.
Never get stuck, your license includes technical support and consultation during your next project. Also, join our online training ready for you and your team. We are here to help you achieve results and improve your pentesting capabilities.
Trusted by technical teams at companies of all sizes around the globe
What the comunity says about Exploit Pack:
"Penetration testing has a lot of repeating tasks, especially when doing similar assignments for clients. For this reason, tools like Exploit Pack help with automating repeating activities. This framework contains over 39.000 exploits, probably much more than one might ever need." - linuxsecurity.expert